 https://unsplash.com/photos/842ofHC6MaI
https://unsplash.com/photos/842ofHC6MaI
Integrating security into your application provisioning process is easy with Imperva’s open source API Composer tool, available on GitHub.
Application programming interfaces (APIs) are the cornerstone of many an enterprise’s core business functionality. These powerful tools streamline development and allow for easy, standardized feature implementation in a wide range of contexts.
Imperva’s on-premise Gateway WAF and Cloud WAF technologies can help protect both external and internally facing business critical applications, but introducing security can not break the current deployment processes used by the business. Adding security into your CI/CD and application provisioning process can be easy when leveraging APIs to do so.
When implementing any integration leveraging APIs, the first step is for the developer to come up to speed with the how to use the API. To streamline that on-boarding process, Imperva has introduced an open-source solution which makes it easy for a developer to interactively test each API call before implementing it in code.
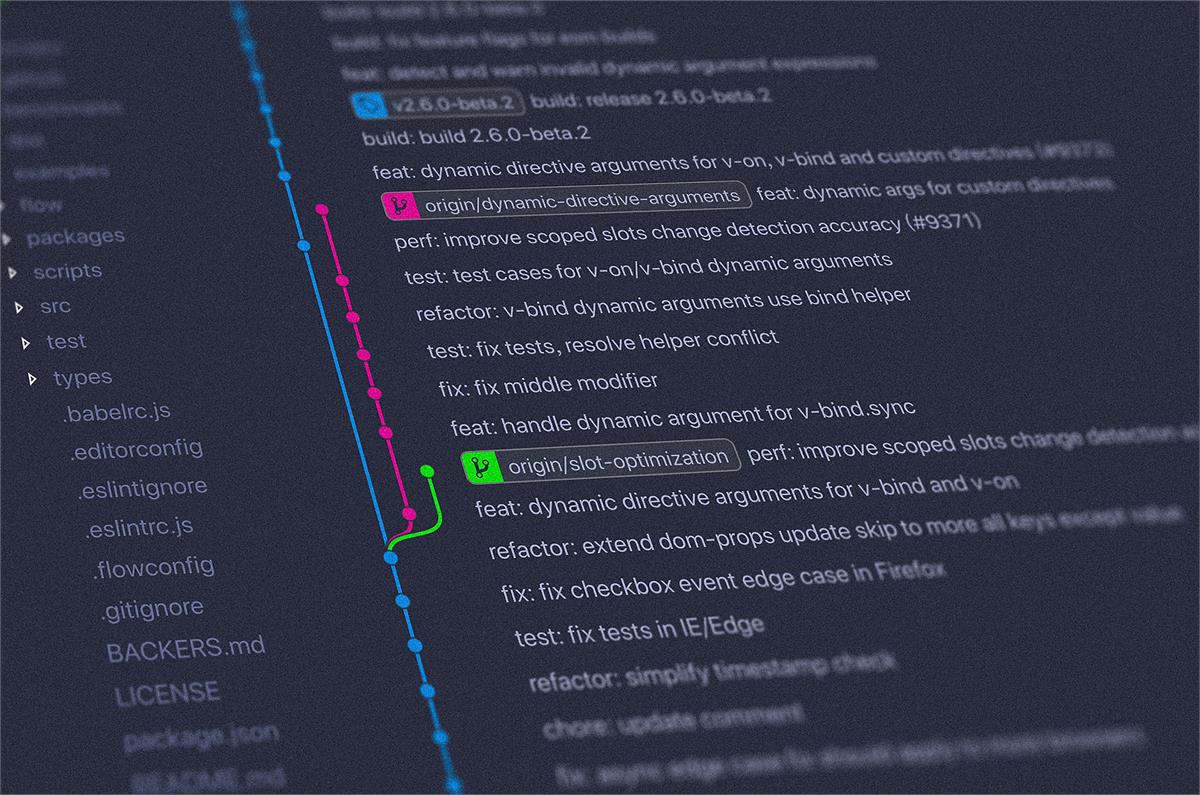
Introducing API Composer: Efficient, On-Demand API Call Generation and Testing
Imperva API Composer gives on-premise Gateway WAF and Cloud WAF users the ability to quickly generate and test API calls interactively pre-populating contextual parameters between calls, as opposed to simply referring to documentation. API Composer is packaged as a container using Docker and Docker Compose, making it possible to get up and running with a single command.
After it’s installed, a user can simply add credentials for a on-premise WAF management server (MX), or for Cloud WAF , and the API Composer will validate those credentials, and enable the user to test against that system live. The composer also allows you to store multiple sets of credentials, making it easy to interchange between multiple MXs or Cloud WAF accounts from the same tool, making it an ideal solution for large, complex enterprise environments.
API Composer automatically loads the schema of the APIs (Swagger or WADL), enabling the user to pick specific API call resources/URLs, and methods to test from dropdowns. These calls are alphabetized, categorized and easy to find. Once a user selects one, the tool will automatically generate a sample cURL request with placeholder names and parameters populated to test directly in a terminal or as guidance for how to implement a particular call in code. Not all API resources/URLs support all methods (POST, GET, PUT, DELETE), and in many cases the combination of parameters will change when using different methods (POST vs PUT, etc) on the same URL. The Composer will dynamically render and populate the appropriate parameters when changing a resource/URL and method on the fly making it easy to test any call without having to sift through documentation.
All you have to do to test a new API call is replace those placeholder names with your own data, and you have a usable request call ready for testing. Since API Composer also generates a cURL request, you can even drop the request straight into a command-line interface application like Terminal and execute it immediately. The entire process takes mere seconds.
API Composer Gateway WAF Examples: Managing the site tree
The Gateway WAF API schema includes dynamic URLs constructed of various values that are specific to the API call that is being executed. Also, the HTTP method maps to the underlying associated action consistent with REST standards; GET is read, POST is create, PUT is update, and DELETE is delete.
For example:
- To retrieve a list of server groups, you would use the GET method and specify the site name in the URL as follows:
GET “/SecureSphere/api/v1/conf/serverGroups/{siteName}”
- To create a server group under a specific site, you would use the POST method and specify the site name, and the desired server group name in the URL as follows:
POST “/SecureSphere/api/v1/conf/serverGroups/{siteName}/{serverGroupName}”
Instead of having to copy and paste these values (like site name and server group name) into the url each time you want to make or test a call, the Composer will actually pull these values down and pre-populate them for you allowing you to easily copy them into the request on the fly. The request url will highlight red if there are any URL placeholders that need values, and when the placeholders are populated, the url turns black and a functional curl example is generated.
Screen Shots:
Once the call is executed, the tool will create a new server group inside the management server. The user can do this live and enjoy immediate results, or drop the automatically generated CURL request into a command-line interface application like Terminal and then test the result in the code itself.
API Composer Cloud WAF Examples: Managing sites
The Cloud WAF API schema consists of a collection of static URLs with different combinations of parameters based on the API call that is being executed. Some of these parameters are dependent on other parameters, and the Composer helps to look those up on the fly making it easy to test interactively.
For example:
- If you are looking to add a new security policy, you will need to specify the site_id, as well as a rule action (block, redirect, etc) and a response code. A list of all available sites with site IDs from that account are rendered on the fly, and any parameter with enumerated values are pre-populated in the form of drop-down lists making it really easy to test calls.
How to Incorporate API Composer Into Your Workflow
The purpose of API Composer is to give developers the ability to extrapolate what calls are available in any given MX management server, test them individually, then take the example requests and run them in the same context they would run when implemented in code. The tool also facilitates the conversion of that result into usable code in whatever language the user needs, such as Python, Java, PHP, or C#.
You can certainly achieve these things without API Composer and potentially using tools like Postman, but dynamically loading the schema based on the version of Gateway WAF, loading Cloud WAF site and account IDs dynamically, the pre-formatting of api calls, and populating the dynamic URL parameters are certainly streamlined with this tool.
If the business has a requirement to automate the provisioning of applications, and the security solution(s) that accompany those applications can not natively support those automation requirements, the business is stuck with the hard choice of managing the process manually or potentially removing security. API Composer empowers organizations to come up to speed quickly and easily to seamlessly integrate security into existing DevOps processes where security moves at the speed of the business.
Related Content:
Automated Certificate Management and Security Policy Migration Made Easy
Transcript and Video from Webinar: GitHub Tools - Imperva API Composer
Incapsula-CLI: An Easy-to-use Interface for Imperva’s Cloud WAF#CloudWAF(formerlyIncapsula)#On-PremisesWAF(formerlySecuresphere)