Find out how one of San Francisco’s most reputable financial service providers keeps its users safe and secure.
The Imperva community is an important source of information, troubleshooting advice, and in-depth guidance for cybersecurity professionals who rely on Imperva technology.
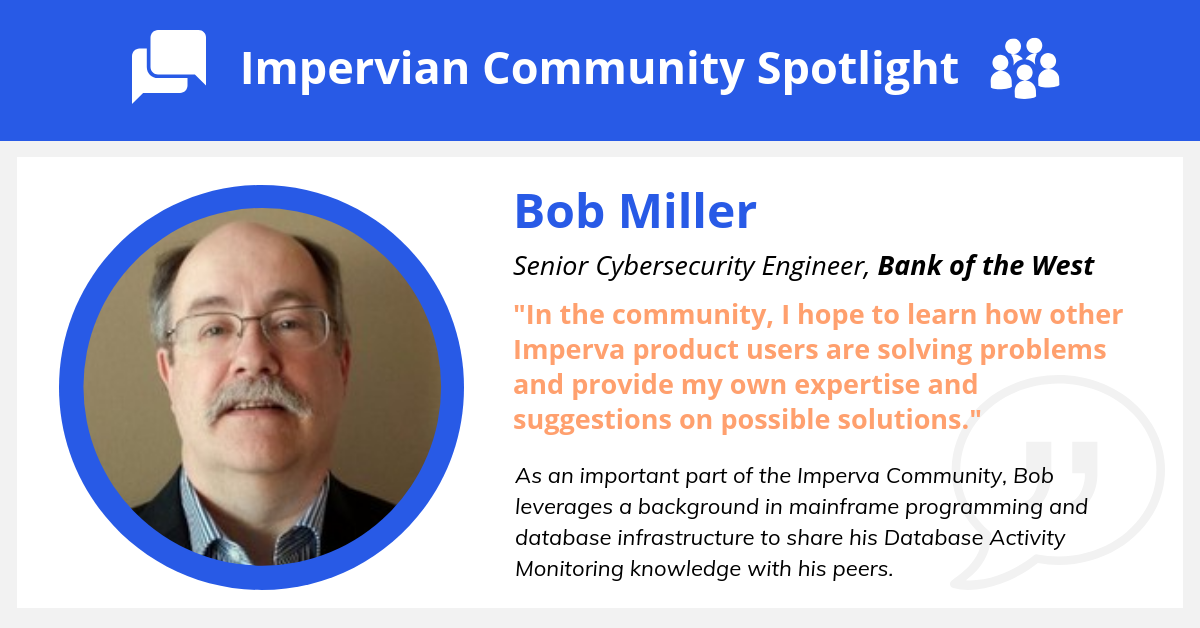
Just ask @Robert Miller, Senior Cybersecurity Engineer at the Bank of the West. Bob leveraged a background in mainframe programming and database infrastructure into a critical role identifying and resolving security vulnerabilities for a bank with 600+ branches and almost 2 million customers.
Introducing Bob Miller
Bob’s first foray into the world of cybersecurity happened on accident. After his early years as a customer engineer working on midrange systems and peripherals, he managed a technology laboratory operating a small datacenter.
In Bob’s own words, “I was basically given two dozen racks of equipment and told to make it all work.” It was in this role that Bob came into contact with Imperva appliances, and had the chance to work closely with some of our database solutions.
Now, Bob specializes in Database Activity Monitoring (DAM) deployment. Proper DAM configuration is the foundation of best-in-class cybersecurity. Bob’s background working with databases and securing database activity helps inform his methodical approach.
Bob Miller’s DAM Tips
As a mainframe engineer who spent years working on mainframes and distributed systems in COBOL – which still accounts for 80% of the world’s actively used code – Bob’s recommendations start at the command line.
“Configuring gateways from the command line is much quicker than going through the menu. I use a spreadsheet to gather than data and dynamically build the commands, then paste it into the command-line interface. This works well when you have multiple gateways to configure. I can complete 9 gateways in 30 minutes this way.”
Highly organized methodologies like Bob’s are key to maximizing efficiency in a busy workplace. Experienced software engineers of all kinds will store their most commonly used code snippets in an easily accessible place – database cybersecurity management is no different in that respect.
While Imperva’s menu makes it easy to navigate complex systems, there are few things faster than pasting already-written code directly into the command line.
Bob also puts special emphasis on one of cybersecurity’s most challenging aspects – the human factor:
“One of the most rewarding parts of the job is identifying opportunities to improve security infrastructure and reduce vulnerabilities; one of the biggest problems is retraining users to keep them from doing the unsecure practices they have been doing for years.”
Bob’s Advice for the New Generation of Cybersecurity Talent
We asked Bob what he’s looking forward to most in the next few years, and his answer was as simple as it was relatable: “Retirement!”
The cybersecurity industry is different now than it was when Bob started writing his first COBOL commands. As a senior engineer with a unique skill set, he feels the impact of the global shortage of cybersecurity talent in today’s workforce.
“Finding individuals that have a broad range of knowledge on the best security practices, operating systems, application development, databases, and scripting is one of the biggest challenges the industry is facing right now.”
If Bob were to go back in time and give himself advice at the start of his career, he would tell himself to move around more and keep interviewing. The same might be said of the newest generation of cybersecurity engineers now entering the workforce – with more than 4 million positions unfilled, there is a deep need for solid security talent in every industry.
But the first snippet of wisdom that Bob would like new security engineers to remember is neither technical nor job market-related. It’s a bit of practical advice:
“Whatever you do, don’t walk up to a system console, start typing, and then say ‘uh-oh’. You will attract a lot of attention very quickly.”
#AllImperva#Impervian Spotlight
#champion#ImpervianSpotlight