
Pic found here: https://unsplash.com/photos/LqKhnDzSF-8
Introduction to Sensitive Data Scanning
Many organizations lack visibility into the sensitive data in their possession. This lack of visibility creates a number of different risks because unprotected data may be exposed to a data breach. Or, a failure to restrict access to sensitive data could place an organization in breach of data protection regulations.
Imperva DAM provides the ability to rapidly and automatically scan an organization’s database for a wide range of sensitive data (including custom, user-defined types). Configuring a scan for sensitive data not only provides visibility into an organization’s stores of this data but also lays the groundwork for implementing audit and security policies in Imperva DAM.
Configuring a Scan
Configuring a scan requires defining the types of sensitive data to look for and setting other parameters for the scan (such as when it should be run). The settings for configuring Scans are located under the Discovery and Classification, the leftmost option in the top ribbon in the console.
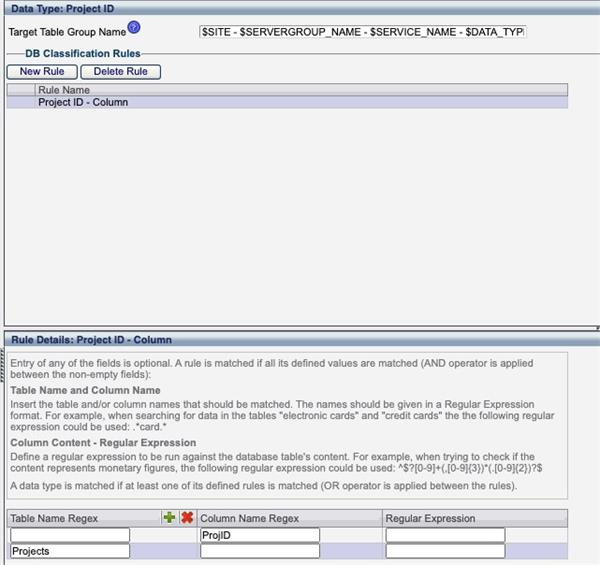
Defining Data Types
The first step in defining a scan is identifying the types of data that the scan should be able to look for. Under the Scans Management tab in the blue ribbon should be a drop-down menu labeled Scope Selection. In this menu, select Data Types Configuration.
Creating a Scan Profile
To create a scan profile, select the Scan Profiles option from the Scope Selection drop-down menu under Scan Management. This will open a window with two tabs.
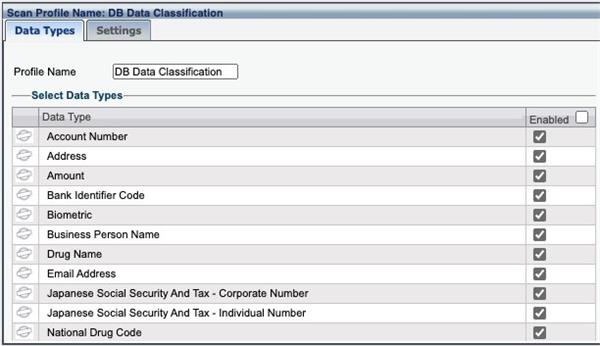
The left tab is labeled Data Types and is shown above. In this tab, the types of data to be included in the scan can be defined based upon the Data Types defined previously. To remove a particular data type from the scan, uncheck the box in its row.
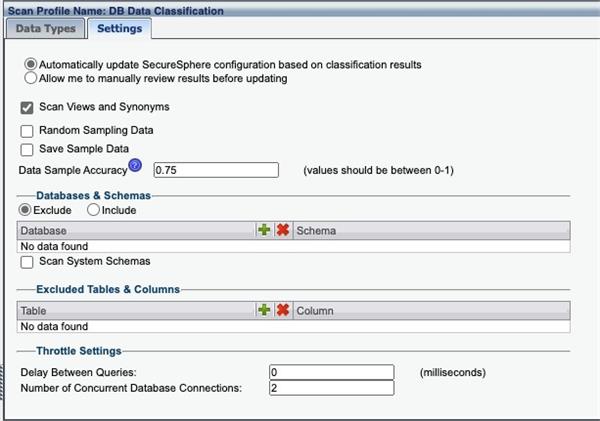
The Settings tab (shown above) provides more configuration options for the Scan Profile. One value of interest here is the Data Sample Accuracy. This value can be set in the range 0-1 and allows users to balance the false positive and false negative rates of a potential scan.
Creating the Scan
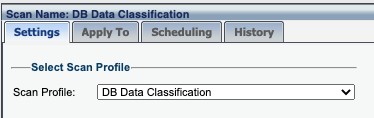
After defining a scan profile, it is time to create the scan itself. In the same drop-down menu as previously, select the Scan option.
The window opened has a number of different tabs:
In the Settings tab, select the previously defined Scan Profile that describes the types of sensitive data to be searched for during the scan.
Apply To: The Apply To tab defines where the scan should be performed. This can include the entirety of a site tree or a subset of it.-
Viewing Sensitive Data
If a scan is run now, it may take some time for the scan to be complete. By monitoring the History tab, it is possible to track the current status of the scan. Once a scan has been completed, the results can be viewed by clicking on the Classified DB Data tab in the Blue ribbon towards the top of the screen.
#DatabaseActivityMonitoring