Using Imperva Data Risk Analytics (DRA) to Identify Data Reconnaissance Efforts
A successful data breach can be extremely damaging to any organization. Companies regularly collect data about their customers in the course of doing business, and a failure to properly secure this data against exposure can cause a loss of customer trust and, potentially, lawsuits and the imposition of penalties by regulatory authorities under data protection laws.
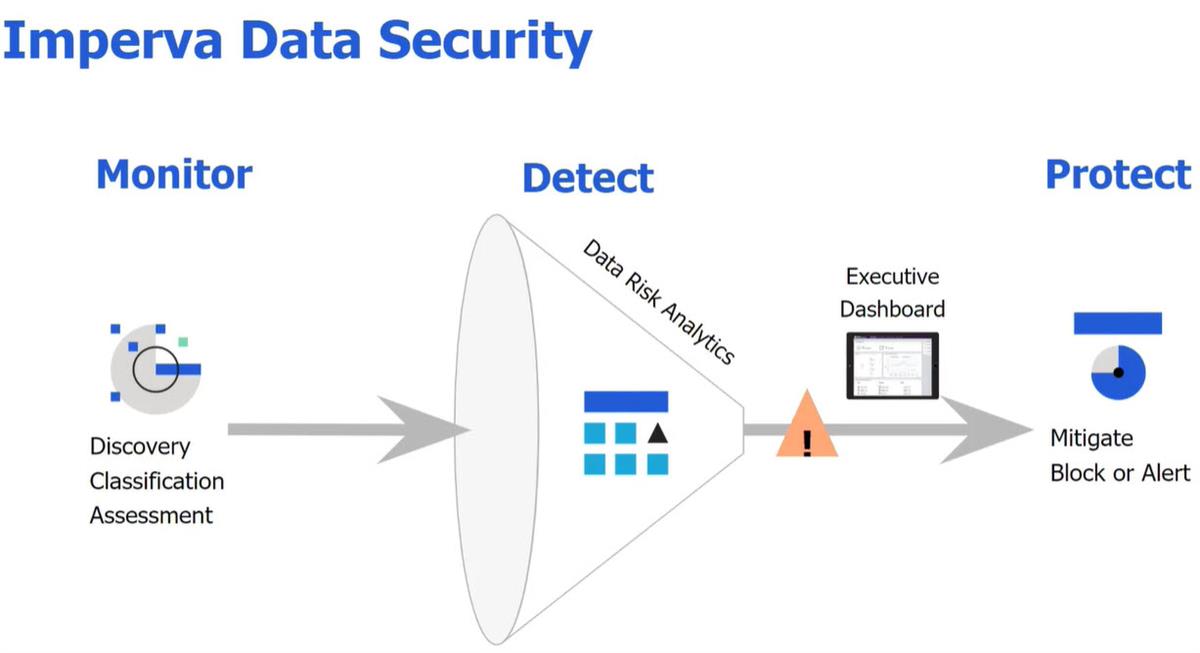
Imperva Data Risk Analytics (DRA) enables organizations to reduce their exposure to potential data breaches. By monitoring access patterns to databases and the data that they contain, it is possible to detect attempted data breaches before the cybercriminal is able to access or exfiltrate sensitive information.
Using DRA to Identify Pre-Breach Reconnaissance
Attempted data breaches can be detected at multiple different points in the cyberattack lifecycle. These include everything from the attacker’s initial attack vector to the final exfiltration of sensitive data.
Before an attacker can access or exfiltrate an organization’s sensitive data, they need to find it first. Imperva DRA includes several issue types dealing with the reconnaissance phase of the cyberattack lifecycle. These issues compare an attacker’s actions to the normal patterns of life for an organization’s databases and alert on or block anything that is anomalous. This enables Imperva DRA to identify novel attacks without impacting the daily business of an organization’s employees.
Excessive Failed Logins
Weak and reused account credentials are a common cybersecurity issue. Cybercriminals regularly perform credential stuffing or brute force password guessing attacks in an attempt to gain access to a particular system.
This can also apply to databases within an organization’s network. While an attacker may have access to the network via one user’s account, this account may lack the access and permissions required to achieve their objectives. However, if the attacker can guess the credentials of an account with the desired permissions, then they can access and exfiltrate data from a database.
The Excessive Failed Logins issue in DRA deals with this particular case. DRA tracks the number of login failed attempts that a particular user usually makes when attempting to access the database and takes action if the number of failed logins in a row exceeds this threshold. This enables the system to detect attempted credential stuffing or password guessing attacks without penalizing users that frequently mistype or forget their password.
Excessive Multiple Database Access
Most organizations have a number of different databases within their network. Some of these databases contain information that would be of interest to a cybercriminal, while others are essentially useless to an attacker. Since exfiltrating massive amounts of data increases an attacker’s probability of detection, it’s important for an attacker to identify useful databases before extracting data from them rather than waiting to sort through the data after it has been stolen.
To accomplish this, a cybercriminal will often start searching through the databases present on a network. This is where Imperva DRA’s Excessive Multiple Database Access issue can detect the intrusion. While employees and systems may access multiple databases within a small period of time, these accesses typically fit standard patterns. An attacker searching for databases to find sensitive data is likely to deviate from these patterns, making it possible to detect and respond appropriately.
Suspicious Sensitive Database Table Scan
A single database can contain a number of different tables. Some of these may contain sensitive and valuable information (user credentials, etc.) while others may be less valuable to an attacker.
After identifying a potentially promising database within an organization’s network, an attacker also needs to determine which tables within this database actually contain the target data. This can require scanning through multiple different database tables using manual commands.
Many of these manual commands are unusual for an application (the primary user of many databases) to perform. For example, an application has no need to ask the number and names of tables within a database or the number of records within a particular table. Imperva DRA monitors for these unusual actions and takes action (raising alerts) if a human user is detected making an unusual number of manual requests regarding sensitive tables within a particular database within a certain period of time.
Machine Takeover
Cybercriminals, when they gain access to systems on a network, typically attempt to expand their influence and footprint in a few different ways. These include both exploiting additional systems on the network and gaining access to new user accounts via compromised credentials.
In a well-secured network, only the correct combination of compromised machines and credentials will allow an attacker access to a database. The database should only be accessible to machines with the need to access it, and access to the database should be restricted to certain users.
The Machine Takeover issue in DRA deals with the case when an attacker identifies a “correct” combination of host and user account but not a “normal” one. For example, a particular user’s workstation may have access to a database, but a request coming from that workstation is using another user’s account. Since this combination of system and account is anomalous, Imperva DRA can flag the access attempt, making it easier to take additional action as required to prevent unauthorized access to the database.
Imperva DRA Detects Data Exfiltration
In any cybersecurity incident - and attempted data breaches in particular - detecting and responding to the attack as quickly as possible is important. Delays in threat detection and response increase the probability that an attacker will successfully access and exfiltrate sensitive data or do additional damage to compromised systems.
Imperva DRA enables analysts to detect attempted data breaches early in the cyberattack lifecycle. Before an attacker can exfiltrate sensitive data, they need to find it within an organization’s networks and the databases that contain it. Imperva DRA can generate alerts regarding the anomalous actions that an attacker takes while performing reconnaissance, enabling a potential data breach to be shut down before it begins.
Data Risk Analytics Overview
To view DRA, you can watch the video 👉 here. You will need to login to the community to watch it. In it you will find:
- A Short Introduction to DRA
- High level Use cases DRA solves
- Advanced Investigation & Tuning
- Tips for investigation
- Tips for tuning
- Tips for mitigating risk and threats
Learn More with Imperva Community
The Imperva Community is a great place to learn more about how to use Imperva cybersecurity technologies like WAF Gateway, Data Risk Analytics, Database Activity Monitoring and more to establish efficient, secure processes for enterprise networks. Rely on the expertise of Imperva partners, customers and technical experts.
Other Relevant Content
In-depth video of Data Risk Analytics